Allow a role to assume another role via AWS Trust Policy
If you're using Awsume or the AWS CLI and want to swap roles, or you have a role that you want to allow another role to inherit, you can need to ensure the services and roles can assume the Role.
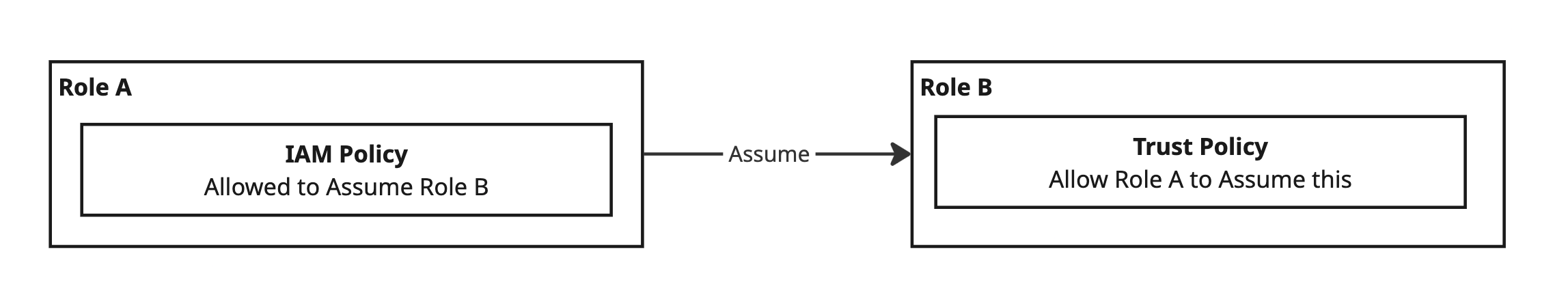
By default AWS does not allow your role to do anything, so you must allow it via permissions. You configure the incoming rules to the destination Role by the Trust Policy on the Role, and the outgoing permissions of the principal via IAM Policies.
Think of the actions your Roles / Users (called Principals) perform as API calls. Consider the permissions model as a big firewall inside AWS. You must allow the actions on your resources for anything to happen.
Changes attempted by your Principals (calling the AWS APIs and that is controlled by the permission) are checked when they go out of the Principal and when they reach the AWS APIs.
In Lambda, you configure which Role the Lambda should execute under. When the Lambda is invoked, the Lambda service will look at the configured Role and do its best to assume the Role via an AWS API call. The assumption attempt will fail if the Lambda is not allowed to assume the role. That is controlled by the Trust Policy on the Role.
In addition to services inside AWS, we can allow Users to assume Roles, and can allow users under Roles to assume other Roles.
Allow AWS Lambda to assume a Role
Given an existing Role, set this Trust Policy with the AWS Service:
{
"Effect": "Allow",
"Principal": {
"Service": "lambda.amazonaws.com",
"AWS": "arn:aws:iam::111122223333:role/my_role"
},
"Action": "sts:AssumeRole"
}
Allow an AWS User to assume a Role
Given an existing Role, set this Trust Policy using the users IAM ARN via the AWS principal:
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::123456789012:user/ExampleUser"
},
"Action": "sts:AssumeRole"
}
]
}
Allow a Role to assume another Role
This works for Principals (like a User) which have assumed an existing Role .
For a Principal that is executing as Role (A) to assume Role (B):
- Role (A) must be granted
sts:AssumeRolepermission (allowed) via a Policy on Role (A) - think of this as "outgoing". - Role (A) must be given permission (allowed) to use the
sts:AssumeRolepermission via the Trust Policy of Role (B) - think of this as "incoming".
Here's an example where we have a Trust Policy setup with two rules:
- AWS Lambda
"Service": "lambda.amazonaws.com"setup to assume the role. - The second statement allows the role
"AWS": "arn:aws:iam::111122223333:role/my_role"to assume the role.
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "AllowLambdaToAssumeThisRole",
"Effect": "Allow",
"Principal": {
"Service": "lambda.amazonaws.com"
},
"Action": "sts:AssumeRole"
},
{
"Sid": "AllowMyRoleToAssumeThisRole",
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::111122223333:role/my_role"
},
"Action": "sts:AssumeRole"
}
]
}